
Key Points: An August 2025 federal court ruling has opened the door for plaintiffs to use alleged inaccuracies or misrepresentations in a company’s privacy policy and other privacy disclosures as the basis for a federal wiretapping claim under the Electronic Communications Privacy Act (“ECPA”).
Unlike state wiretapping claims like CIPA, class action plaintiffs can file ECPA claims nationwide and they can carry statutory damages of $100 per day of violation or $10,000, whichever is greater. Plaintiffs’ firms are increasingly leading with ECPA claims in demand letters and class action complaints.
Companies can take steps to help insulate themselves from litigation by assessing and modifying their privacy policy and other data processing disclosures.
Introduction
Any company with a privacy policy that operates a website using so-called tracking technologies such as pixels, cookies, software development kits, or third-party analytics tools (which is practically every company) should be aware of the real class action risk associated with the federal wiretapping law known as the Electronic Communications Privacy Act (ECPA or Wiretap Act) and its “crime-tort” exception. We have data mined and analyzed thousands of privacy lawsuits using AI to track plaintiff lawyers’ allegations and patterns.
In short, class action plaintiffs have alleged that inaccuracies in privacy policies and other privacy-related disclosures (e.g. consent banners) tied to the use of website tracking technologies violate the ECPA under its crime-tort exception. Many of the privacy disclosures cited by plaintiffs in support of their claims are commonly found in websites’ privacy policies across the internet. The ECPA allows for statutory damages of the greater of $100 per day of violation or $10,000. Plaintiffs can file ECPA lawsuits in any state (not just those states with all-party consent wiretapping laws). And unlike earlier iterations of tracking-tech litigation, these allegations turn your own privacy disclosures, including your privacy policy and consent banner statements into the plaintiffs’ primary exhibits.
The blueprint for this application of the crime-tort exception was laid out in order issued on Aug. 4, 2025 on a motion to dismiss, where a federal judge out of the Northern District of California ruled that a footwear retailer’s alleged misrepresentations in its privacy policy could supply the predicate tort needed to state a Wiretap Act claim. (hereinafter the “ECPA Privacy Policy Order”). Plaintiffs have filed dozens of complaints since September 2025 replicating this formula in their pleadings.
Part One of this two-part post explains how we got here and what the plaintiffs’ ECPA crime-tort formula looks like. In Part Two, using data we’ve culled and analyzed from more than 12,000 complaints filed between 2015 and March 2026, we will explore what class actions plaintiffs have done since the ECPA Privacy Policy Order, the types of allegations they made concerning privacy misrepresentations, and importantly, what companies can do right now to reduce their litigation risk.
1. The ECPA Privacy Policy Order
The CIPA and All-Party Consent State Litigation Wave
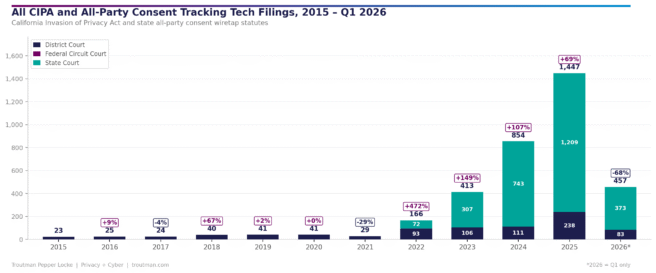
Beginning in earnest around 2022 and accelerating through 2024 and 2025, plaintiffs’ attorneys filed more than approximately 3,500 lawsuits under various U.S. state all-party consent wiretapping laws. Approximately 3,291 of those filings were made in California state and federal courts alleging violations of the California Invasion of Privacy Act (CIPA).
Plaintiffs claim that when a website deploys a third-party tracking pixel or similar website tracking technology (e.g., the Meta Pixel, TikTok Pixel, or Google Analytics tag), the pixel intercepts the “contents” of a visitor’s communications in transit. Many of the initial lawsuits targeted session replay, which records the movements of website users while visiting a site. Because California is an all-party consent state, plaintiffs argued this interception violated CIPA unless the website visitor consented to the transfer of data to third parties through alleged trackers.
Later, plaintiffs expanded their CIPA theory to include the statute’s pen register and trap-and-trace device provisions. Under this theory, Plaintiffs contend the collection and transmission of website-related metadata to third parties via tracking technologies is the equivalent of operating a pen register or trap and trace device capturing dialing, routing, addressing, and signaling information, such as originating and destination phone numbers, call duration, and session identifiers. This approach opened a fruitful avenue because virtually every tracking technology transmits the visitor’s IP address and HTTP request headers at minimum, and typically far more granular interaction data reflecting the visitor’s browsing behavior and engagement with the site.
Potential exposure under CIPA is significant: statutory damages of $5,000 per violation. Multiplied across a class of website visitors, the numbers grow quickly into the tens or hundreds of millions of dollars. Many of these cases progressed past motions to dismiss and demurrers, and some moved through class certification. One high profile case went to a jury trial in 2025, and the losing defendant is now potentially facing astronomical damages.
This has exacerbated the pressure for early settlements, and many companies have settled pre-lawsuit demand letters. Plaintiffs’ attorneys have continued to send out tens of thousands of demand letters alleging CIPA violations and offering nuisance-value settlements. These settlements, in turn, have funded further litigation, and more in-court victories for the plaintiffs’ bar.
Defense Wins
CIPA litigation court rulings, however, have not been a one-way street for plaintiffs. Courts have split on fundamental questions: Does a tracking pixel actually intercept the “contents” of a communication? Is the pixel provider a “third party” eavesdropper, or is it a “party to the communication” because the third party is simply an extension of the website and their technology the equivalent of a tape recorder? Was any message “intercepted while in transit” when the user’s browser sends a direct message to the pixel’s servers?
Several courts handed defendants significant wins. In November 2025, the Third Circuit held that a third-party tracking company was not a third-party eavesdropper because it received information directly from users’ browsers and not as an interception. In June 2025, the Ninth Circuit held that a party to a communication cannot eavesdrop on itself. A month later, the Night Circuit ruled that CIPA § 631(a) only applies to “telephone wire, line, cable, or instruments” and not to communications through the internet. Two federal courts in the Northern and Central districts of California also dismissed CIPA claims in June 2025 based on Article III standing. Meanwhile, also in 2025, the California legislature advanced SB 690, which proposed an amendment to CIPA to exclude tracking technologies used for “commercial business purposes.” This bill did not pass in 2025, but was put on a two-year track and may be reconsidered in 2026
These defense wins did not kill tracking technology litigation, but they created some level of uncertainty for plaintiffs and a desire to avoid worse caselaw. This appears to have incentivized plaintiffs’ counsel to look for other tools and theories for bringing tracking technology claims, which lead us to the ECPA.
The ECPA: National Tracking Technology Wiretap Act Exposure
The ECPA’s crime-tort exception. Like CIPA, the 1986 ECPA prohibits the intentional interception, disclosure, or use of electronic communications. Unlike CIPA and other all-party consent states, the ECPA is a one-party consent statute. Since a website operator is always a party to the communication and consents to tracking tools it installed on its website, “consent” would seem to provide a complete defense.
However, there is an exception to this defense: consent does not apply if the interception was made “for the purpose of committing any criminal or tortious act in violation of the Constitution or laws of the United States or of any State.”[1]
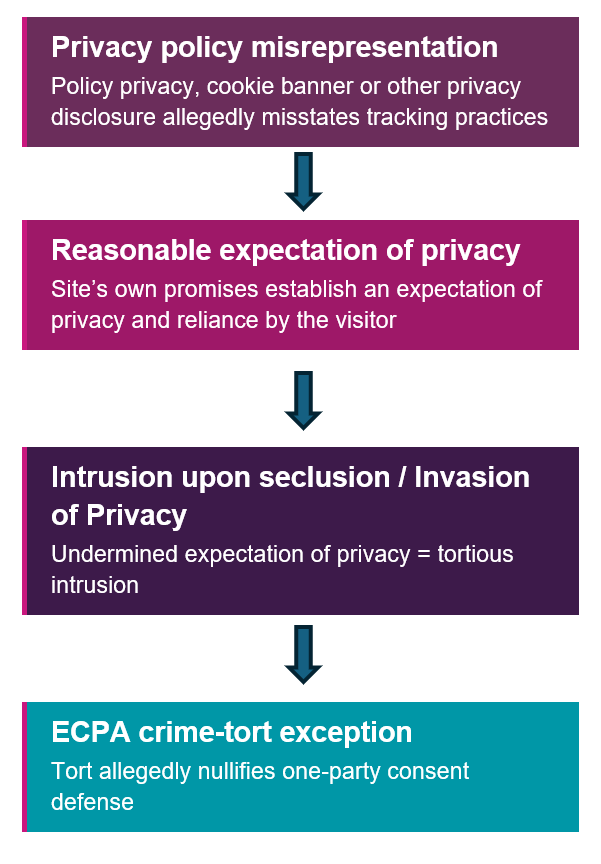
This is the “crime-tort exception” that supplies plaintiffs with a private right of action under the ECPA for alleged privacy policy inaccuracies and other privacy violations (e.g., HIPAA, GLBA, CCPA, and others). To establish the crime-tort exception, plaintiffs must show: (1) a third-party tracking tool intercepted electronic communications (often uncontested at the pleading stage); and (2) the interception was made “for the purpose of” committing some independent crime or tort beyond the act of interception itself.
The health care industry targeted for alleged HIPAA violations. For several years, the crime-tort exception was most often used in health care cases. Plaintiffs alleged that hospitals and health systems that deployed tracking pixels on their websites transferred protected health information (PHI) in violation of HIPAA. Many cases focused on search bars and forms that site users filled in that could include heath care-related information that arguably constitutes PHI. Some alleged that URLs obtained by third party tracking companies contained PHI. The alleged HIPAA violation served as the “criminal or tortious act” triggering the ECPA crime-tort exception.
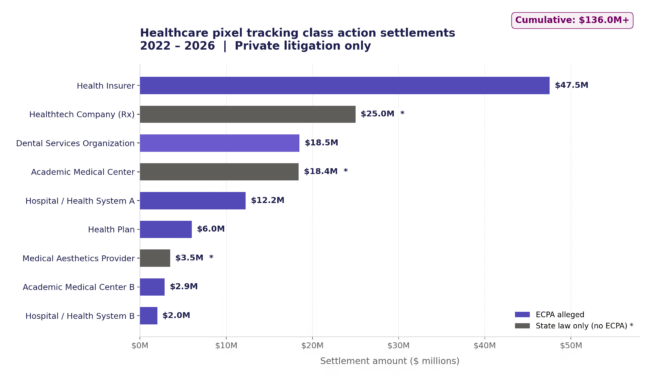
This theory gained traction. In February and June 2025, federal district courts in Illinois and New York allowed ECPA claims to survive past motions to dismiss where HIPAA violations were alleged as the predicate for the crime-tort exception. Significant class settlements followed, with high-profile health care tracking technology settlements exceeding $135 million between 2023 and March 2026. Some relied on state wiretapping laws, but ECPA allegations were also in play:
And like CIPA claims, the number of ECPA lawsuits grew from 2022-2024, and then exploded in 2025:
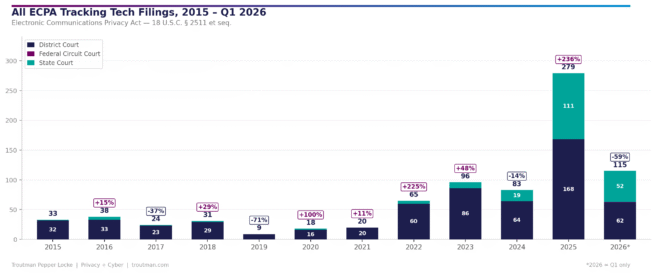
After a 235% increase in lawsuit filings with ECPA claims in 2025, we are on pace for approximately 460 new lawsuits in 2026, which would be another 60% increase year-to-year. Approximately 70% of the lawsuits alleging ECPA violations were filed as class actions. Through 2025 a large portion of these suits were filed against health care companies and tied to HIPAA, which seemed to limit the ECPA’s reach. Then came the ECPA Privacy Policy Order in August 2025.
2. The ECPA Crime-tort Privacy Violation “Formula”
The Case
The ECPA Privacy Policy Order arose out of a class action lawsuit against an online shoe retailer defendant, not a HIPAA-regulated health care company. The defendant does not process PHI on its website, but was sued nonetheless under the ECPA for the use of tracking technologies on its website. The class action complaint alleged that the retailer deployed tracking technologies from six different companies on its website. These tools allegedly intercepted visitors’ browsing activity, purchase history, and other personally identifiable information, and transmitted that data to third parties. To overcome the one-party consent exception to liability under the ECPA, plaintiffs argued the interception was for the purpose of committing the tort of intrusion upon seclusion. To support their claim, plaintiffs looked to the retailer’s privacy disclosures and pointed out alleged misrepresentations and inaccuracies, including the following:
- The privacy policy stated: “[The retailer] collects information through cookies and beacons … but none of the information collected through cookies or beacons is personally identifiable.”
- A separate privacy policy disclosure stated: “Our usage of cookies is in no way linked to any Personal Information while on our site.”
- The cookie banner promised that “Necessary Cookies” “do not store any personally identifiable information” and that “Targeting Cookies” “do not store directly personal information.”
The plaintiffs alleged these representations created a reasonable expectation of privacy for website visitors, which is a necessary element for an intrusion upon seclusion claim. They also alleged that those representations were false, thereby undermining that expectation.
Judge Lin’s Ruling (August 4, 2025)
On August 4, 2025, Judge Rita F. Lin issued the ECPA Privacy Policy Order on the defendant’s second motion to dismiss. The Wiretap Act claim survived. The key passage:
… Plaintiffs allege that [the retailer] intended to disclose its customers’ personally identifiable communications — which it had promised not to collect or use — to third parties so that it could deliver targeted ads to its customers. [The retailers] alleged disclosure and use of Plaintiffs’ personally identifiable information for advertising, in contradiction [of] the commitments it made in its privacy policy, can plausibly constitute a further invasion of privacy beyond the act of intercepting the information alone.
Judge Lin cited the HIPAA-related ECPA cases in support of her decision: “[t]he allegations are analogous to the purpose of engaging in a HIPAA violation, which courts consistently find constitutes an independent prohibited purpose [under the ECPA’s crime-tort exception].” Since Judge Lin’s August 2025 order, plaintiffs have filed another amended complaint and survived another motion to dismiss, in part. Defendants filed their answer in February 2026, and plaintiffs’ motion for class certification is due at the end of May 2026.
The Formula
What the ECPA Privacy Policy Order established is a replicable formula for stating a cause of action based on the ECPA’s crime-tort exception against any company that operates a website and makes certain privacy disclosures:
Part Two: Mechanics and Mitigation
We have seen this formula used and alleged repeatedly by multiple law firms (both in demand letters and class action complaints). Understanding their approach is key to directly mitigating risk. With the foregoing as prologue, Part Two of this series explores what has happened with tracking technology litigation since the issuance of the ECPA Privacy Policy Order. We have interesting data and insights that reveal a significant increase in lawsuits alleging ECPA claims across the nation. We will identify the types of privacy misrepresentations plaintiffs are alleging, and how privacy policies, cookie policies, and cookie banner disclosures can be fixed to help reduce litigation risk.
[1] 18 U.S.C. § 2511(2)(d).