
Key point: (1) Plaintiffs who expand their class definition beyond the complaint risk losing both certification and their class representative on limitations grounds; (2) Banners that require users to interact before accessing website may be sufficient to establish consent; (3) What makes tracking “highly offensive” is becoming clearer; (4) the “in transit” requirement continues to divide courts; (5) Courts demand more than labels to survive a standing challenge.
Welcome to our monthly update on how courts across the U.S. have handled privacy litigation involving website tools such as cookies, pixels, session replay, and similar technologies. In this post, we cover decisions from April 2026.
Many courts are currently handling data privacy cases across the U.S. Although illustrative, this update is not intended to be exhaustive. If there is another area of data privacy litigation you would like to know more about, please reach out. The contents provided below are time-sensitive and subject to change. If you are not already subscribed to our blog, consider doing so to stay updated. If you are interested in tracking developments between blog posts, consider following us on LinkedIn.
1. Plaintiffs who expand their class definition beyond the complaint risk losing both certification and their class representative on limitations grounds.
A Northern District of California court’s decision in a consolidated putative class action involving a social media company’s pixel-based collection of tax-filing data offers defendants a significant procedural weapon against class certification in tracking technology cases. When plaintiffs broaden their proposed class definition at the certification stage to include individuals not covered by the original complaint, they may inadvertently expose those individuals to statute-of-limitations defenses such that individualized inquiry can swamp the common questions needed to sustain certification under Rule 23(b)(3).
In that case, the plaintiffs filed a putative class action alleging the defendant used its pixel to collect sensitive tax-filing information from users of two online tax preparation services. The operative complaint proposed classes composed of individuals whose “tax filing information” was obtained by the defendant from those services, with allegations focused on sensitive financial data like income, refund amounts, filing status, and the names of dependents. When plaintiffs moved for class certification, however, they abandoned that definition and instead proposed certifying classes consisting of anyone who visited either tax preparation service’s website during the relevant periods and whose data appeared in the defendant’s internal database. This newly adopted definition swept in individuals from whom the defendant collected nothing more than IP addresses, browser information, geolocation data, or generic page URLs bearing no relationship to tax-filing activity.
That expansion proved fatal on multiple fronts. First, the court disposed of the classes related to one of the two tax preparation services by finding that the only named plaintiff who used that service had no evidence in the defendant’s database confirming that any of her data had actually been collected. Without standing, those classes could not be certified. The court similarly denied certification of all proposed classes seeking injunctive relief under Rule 23(b)(2) after finding that none of the named plaintiffs could demonstrate a present risk of future data collection because the record showed the defendant had not collected any named plaintiff’s data for several years.
The more consequential ruling, however, addressed the remaining classes under Rule 23(b)(3). The court found that plaintiffs satisfied all four Rule 23(a) prerequisites (numerosity, commonality, typicality, and adequacy) but denied certification because individualized statute-of-limitations inquiries threatened to overwhelm the common questions at the core of plaintiffs’ California wiretapping claims. The limitations period for all such claims is one year, and the proposed classes were anchored to data collection ending several years prior, placing every claim well outside the limitations window. Although the filing of a class-action complaint tolls the limitations period for all members of the class as defined in the complaint under the Supreme Court’s American Pipe tolling doctrine, that applies only to individuals whose claims fall within that definition. Because the original complaint defined the class by reference to the collection of tax-filing information, it excluded from that definition individuals for whom the defendant collected only generic browsing data. Those individuals’ claims would be time-barred, and determining which class members fell on which side of that line would require a file-by-file review of roughly nine terabytes of data. The court found this sufficient to deny class certification.
As a rare class certification decision in the adtech privacy litigation landscape, this decision provides several practical lessons for defendants facing tracking tech claims. First, defendants should press plaintiffs in discovery to produce a workable, record-supported methodology for identifying which class members’ data actually implicates the legally significant category of information at the heart of the complaint; the inability to do so efficiently can defeat predominance even where all four Rule 23(a) requirements are satisfied. Second, where a named plaintiff’s own data fails to reflect the core alleged harm, defendants should develop that evidentiary record and use it both to challenge standing at the individual level and to argue that plaintiffs cannot propose an adequate representative for any narrowed class. Third, defendants seeking to defeat injunctive certification should build the record on whether any named plaintiff faces a concrete risk of future harm because past collection alone, with no evidence of ongoing or likely future collection, will not satisfy Rule 23(b)(2). Finally, this decision serves as a reminder that defendants in tracking technology cases should scrutinize whether the proposed class definition at certification is materially broader than the class alleged in the complaint and, if so, immediately analyze whether that expansion exposes putative class members to limitations defenses that were tolled only for the narrower original class.
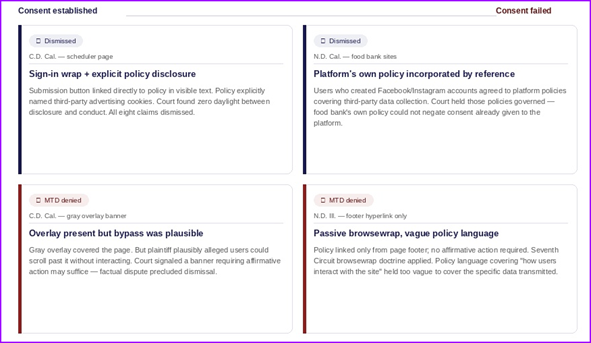
2. Banners that require users to interact before accessing website may be sufficient to establish consent – but only if there are no factual disputes about whether users could bypass them
April’s decisions collectively draw a cleaner line than prior months between banners that work and banners that don’t. A banner that demonstrates users are forced to interact before accessing the website is the gold standard, but defendants cannot cash in on that architecture if the plaintiff plausibly alleges the barrier was illusory. Where the banner held up, it was because users had no path forward without engaging with it and the policy they agreed to explicitly covered the challenged conduct. Where it didn’t, either the mechanism was too passive to constitute assent or a factual dispute existed over whether users could simply scroll past it.
An early decision from the Central District of California sits at the center of this takeaway. The court rejected the argument that the banner was insufficiently conspicuous, finding the gray overlay covering the rest of the site was enough to put users on notice. The court nonetheless denied the motion to dismiss because the plaintiff plausibly alleged that users could bypass the banner entirely by scrolling down. The court signaled that if the overlay architecture actually requires affirmative action (customizing preferences or clicking the X) before the site becomes accessible, that may be sufficient to establish consent.
A second decision from the Central District of California illustrates what a winning consent defense looks like. The scheduler page displayed a sign-in wrap directly below the submission button, with hyperlinked terms in blue text the court found difficult to miss. The privacy policy to which it linked explicitly disclosed that third-party advertising cookies would be placed and used to target users across sites. The court found no daylight between what was disclosed and what occurred and dismissed all eight claims after finding the plaintiff consented to the behavior about which it now alleged was unlawful.
A companion April 27 decision from the Northern District of California extended this logic in a direction worth watching. In this case, the plaintiffs alleged they had visited the websites of four nonprofit food banks and used a map to locate food assistance resources, entering information such as their home addresses and, in some instances, answering questions about age, disability status, mobility, and financial hardship. The complaint alleged the food banks embedded a social media pixel tool on their websites, which captured user interactions and transmitted the data to the social media company, who then linked it to plaintiffs’ social media accounts and used it to serve targeted advertisements related to plaintiffs’ financial hardships.
The court found those plaintiffs who had created Facebook or Instagram accounts (and thereby agreed to the platform’s own privacy and cookies policies) could not claim they were surprised to learn the platform collects data from third-party websites for advertising purposes. The court incorporated those policies by reference, found they covered the alleged conduct, and dismissed the claims. The court rejected the plaintiff’s arguments that the food banks own privacy policies negated any finding of consent because those policies promised not to share user data with third parties.
An April 20 decision from the Northern District of Illinois sits at the other end of the spectrum. In that case, the defendant’s website contained a hyperlinked privacy policy that was accessible from the bottom of every page. The court found the website’s design did not require any affirmative action by the user and the banner was therefore considered a “browsewrap agreement” and likely unenforceable under Seventh Circuit precedent. The court also found the policy’s language, which covered “information about how [users] interact with the Site” was too vague to clearly encompass the specific scheduling data transmitted to the third party.
Taken together, these decisions reiterate that a consent mechanism that requires affirmative interaction (whether by checking a box, clicking a button, or even clicking an X on the banner) and explicitly discloses the specific challenged conduct in the linked privacy policy is likely enough to establish consent and defeat wiretapping claims.
3. What makes tracking “highly offensive” is becoming clearer: cross-platform profiling and sensitive context matter while single-site behavioral data generally does not.
April’s started drawing a workable line around the “highly offensive” element after Popa. In an April 1 decision from the Central District of California, the plaintiff alleged that when she visited a website to purchase a gift card, she opted out of tracking technologies by selecting the “required only” option on the banner. The plaintiff alleged, however, that the defendant had already caused third-party cookies and tracking tech to load on her device before the banner even appeared. The plaintiff argued this amounted to a “misrepresentation” and satisfied the “highly offensive” element of an invasion of privacy claim. The court disagreed, finding the alleged misrepresentation went only to whether the plaintiff had a reasonable expectation of privacy in the first place. It could not do “double duty” by also rendering the intrusion highly offensive.
Relying on the Ninth Circuit’s guidance from Popa, this district court judge held there are two primary ways tracking technologies may result in “highly offensive” conduct. “First, the information collected could be especially sensitive, for example health or financial information. . . . Second, the scope of the collection may be so broad, for example by tracking a Plaintiff’s activity across other websites, that it renders the tracking highly offensive.” Because the complaint did not allege either situation, the court found the conduct was not highly offensive and that the plaintiff had failed to establish standing. Although this decision centered on whether the plaintiff had alleged Article III standing, the decision is also applicable to claims for invasion of privacy, intrusion upon seclusion, and whether those claims are established to serve as the predicate for the crime-tort exception in Electronic Communications Privacy Act (ECPA) cases.
Other April decisions provide further guidance. First, two decision from the Northern District of California reiterate when collection may be “highly offensive.” In an April 21 decision from the Northern District of California, the plaintiffs alleged that a chip embedded in their smart televisions intercepted their video-viewing data in real time, capturing what they watched on cable and streaming services, and used that data to build profiles segmented by political leanings, and then sold those profiles to advertisers. The court found those allegations cleared the highly offensive threshold. In another decision that issued about a week later, the plaintiff alleged a software development kit (SDK) embedded in a dating app for people interested in same sex relationships silently collected the plaintiff’s precise geolocation, device fingerprints, mobile advertising ID, and other identifying data, routed it through identity resolution services that linked it to his real-world identity, and appended it to persistent profiles containing sensitive inferences about health conditions, substance use, and other intimate characteristics. Once again, the court found the collection was “highly offensive” and denied dismissal.
In contrast, an April 27 decision also from the Northern District of California held there was no harm from mere inferences. In this case, which is also discussed in the takeaway above, the plaintiffs alleged they visited nonprofit food bank websites. The court found that disclosing that someone accessed food-resource information on a public website is not similar to revealing that someone applied for welfare, and that California Invasion of Privacy Act (CIPA) violations based on disclosing home addresses and website use do not constitute a concrete injury in fact.
Collectively, these decisions establish that when collection includes sensitive information directly (rather than merely inferences) or is broadly across multiple websites, the “highly offensive” standard is likely to be met. When the collection is limited to a single website’s behavioral tracking, however, defendants have a strong argument to defeat an invasion of privacy claim.
4. While the “in transit” requirement continues to divide courts, April decision show the path to surviving dismissal.
The in-transit split deepened in April. Courts that let claims survive pointed to specific technical allegations about how data was duplicated and transmitted before reaching its destination. Courts that dismissed found conclusory “real time” language insufficient. One court went further, finding the complaint’s own allegations about server-side processing contradicted the plaintiff’s interception theory.
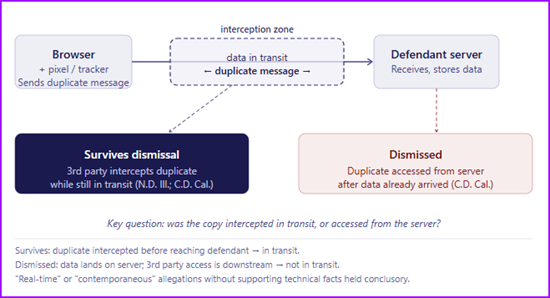
On the dismissal side, one court granted the motion on the § 631 claim after finding the plaintiffs’ allegations of “real time” interception were nothing more than conclusory statutory parroting. The court also found that the plaintiffs’ more specific allegations worked against them as the complaint described how the defendant processed and stored data on its own servers before using it to build audience profiles and serve advertising. The court held the complaint therefore alleged contents were read after transmission, not during it. In an April 27 decision from a court in the Central District of California also dismissed a wiretapping claim on in-transit grounds. That case involved a hair transplant company’s scheduling page, where the court found the plaintiff’s allegation that pixels “contemporaneously” intercepted communications to be a conclusory recitation of the legal standard rather than a factual showing of how that interception could have occurred while data was still in transit from the plaintiff to the defendant.
On the survival side, two decisions demonstrate what sufficient pleading looks like, and how it can conflict with the authority discussed above. In an April 20 decision from the Northern District of Illinois, the court found the plaintiffs adequately alleged contemporaneous interception by pleading that tracking pixels immediately duplicated the information plaintiffs intended to send solely to the defendant before the defendant ultimately received it. The court analogized those allegations to Seventh Circuit precedent involving a server copying incoming emails before they reached the recipient’s inbox. But a decision from a court in the Central District of California denied a motion on the “in transit” requirement after finding “[a]llegations of real-time interception are sufficient to show the messages are intercepted while ‘in transit.’ . . . Plaintiff’s allegations that the Third Parties’ trackers ‘simultaneously’ transmit duplicates of communications to the Third Parties’ servers adequately pleads the elements of a Clase 2 violation.”
The in-transit requirement is one of the more actively contested issues in AdTech litigation right now, and April’s decisions leave the doctrine in an unsettled state. The dismissal courts are applying an increasingly demanding standard where conclusory invocations of “real time” or “contemporaneous” interception are not sufficient while the survival courts, by contrast, are still accepting that same language as sufficient.
5. Courts demand more than labels to survive a standing challenge.
Complaints that fail to allege what was transmitted, to whom, and why it caused harm are vulnerable to dismissal before defendants ever reach the merits. First, in an April 23 decision from a Southern District of California court, the plaintiff alleged that after he booked a dental appointment on the defendant’s website, the plaintiff began receiving targeted advertisements for dental-related products and services. The court held the plaintiff failed to establish Article III standing because the plaintiff failed to allege the specific nature of the dental services he scheduled. The plaintiff argued he omitted that information to protect his privacy, but the court was unpersuaded, finding that without knowing what information the plaintiff actually disclosed (and thus what the defendant allegedly transmitted to the third-party platform), the court could not assess whether any concrete harm had occurred.
An April 27 decision from a Central District of California court also dismissed the complaint after finding the plaintiff failed to establish standing under Article III. The plaintiff in that case alleged they had visited the website for a hair restoration company to schedule a consultation through the website’s scheduler page. The plaintiff further alleged they entered personal information, including their name, email address, and home address, but alleged only that the defendant transmitted the “event” of the plaintiff submitting the scheduling form. The court rejected the plaintiff’s argument that he was harmed because the disclosure deprived him of the value of his “health data,” finding the complaint did not allege that any information that he entered into the scheduling form — health-related or otherwise — was disclosed to third parties. The court also rejected the argument that merely submitting the scheduling form itself is sufficient to constitute “health data” about the plaintiff because the complaint did not allege the plaintiff ever became a patient, attended any appointment at one of defendant’s clinics, or paid the defendant for any medical services whatsoever.
Similarly, an April 6 decision from a court in the Northern District of California held the plaintiff failed to establish standing in a complaint that alleged the use of tracking technologies that captured IP addresses, device type, and browser type violated California’s trap and trace law. The court held vague references to “unique and persistent identifiers” and “audience segments,” without elaboration on what those identifiers actually revealed, could not fill the gap.
Finally, in contrast to the above decisions, an April 20 decision from court in the Northern District of Illinois held the plaintiff’s allegations were sufficient to establish because the complaint included many of the details the April 27 decision lacked, including not only that the appointment was scheduled, but also the date, the name of the treating clinician, and the state in which they were licensed.
The contrast between the Illinois decision and the three California dismissals is useful. Where the complaint does not allege the details of the information that is transmitted or how that information was used, defendants should consider a motion to dismiss under Rule 12(b)(1).